Set up an OneLogin connector
This is an updated and improved version of the OneLogin connector! If you’re setting up OneLogin with ConductorOne for the first time, you’re in the right place.
Capabilities
| Resource | Sync | Provision |
|---|---|---|
| Accounts | ✅ | |
| Roles | ✅ | ✅ |
| Groups | ✅ | |
| Application assignments | ✅ | |
| Privileges | ✅* |
*You can opt into syncing privilege data; this is not synced by default.
Gather OneLogin credentials
Configuring the connector requires you to pass in credentials generated in OneLogin. Gather these credentials before you move on.
A user with Administrator or account owner access to your OneLogin account must perform this task.
Create an API credential
Sign into OneLogin as an Account owner or Administrator.
Navigate to Developers > API Credentials.

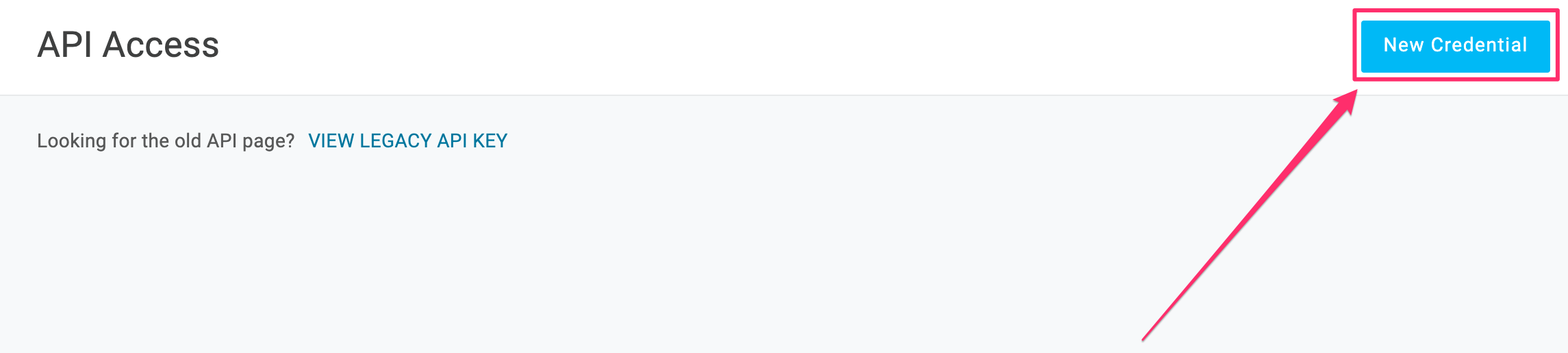
Click New Credential
Give the API credential a name, such as ConductorOne.
Select the Manage all scope.
Click Save.
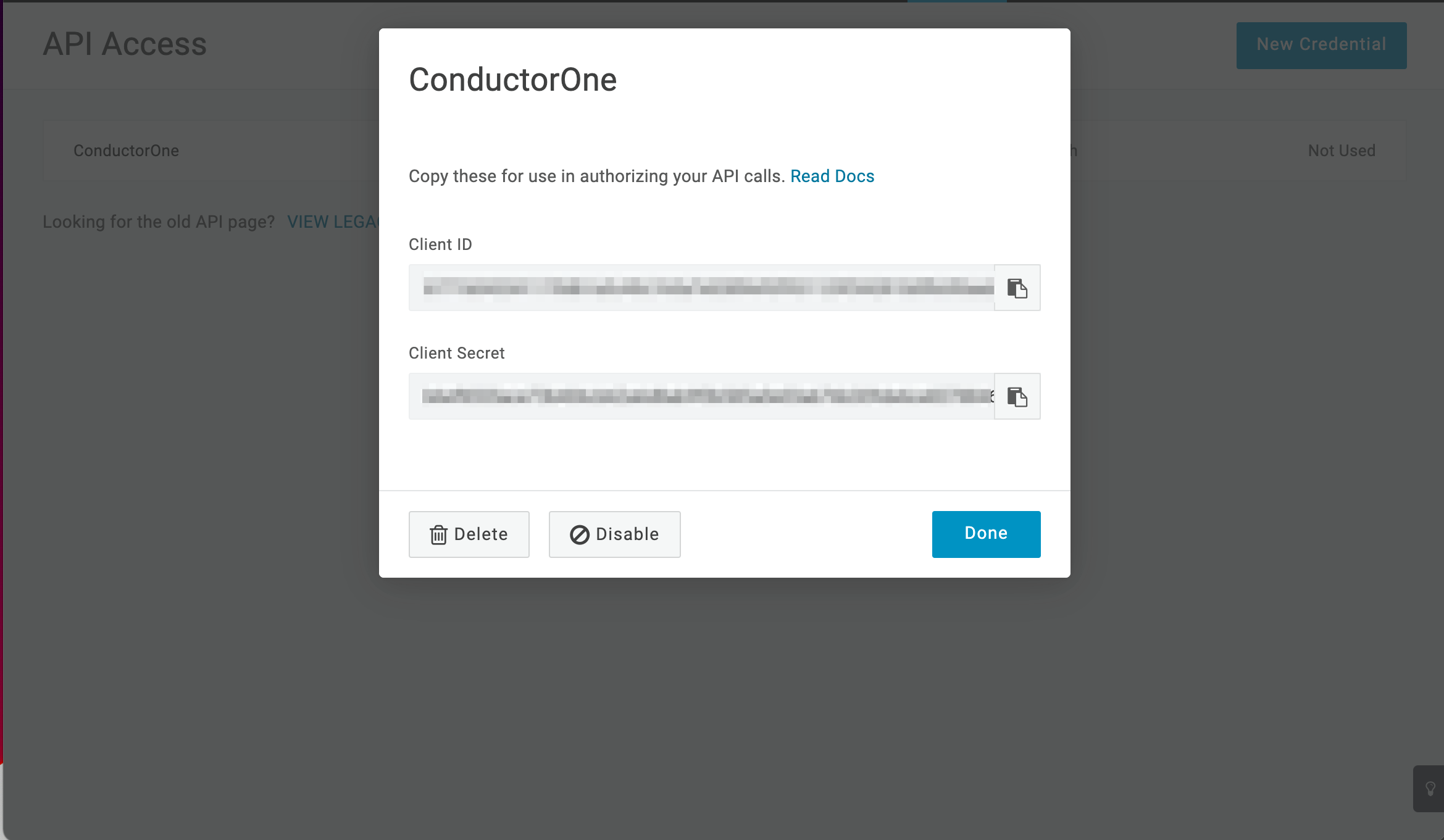
When the new API credential is created, copy and save the Client ID and Client Secret.
That’s it! Next, move on to the connector configuration instructions.
Configure the OneLogin connector
To complete this task, you’ll need:
- The Connector Administrator or Super Administrator role in ConductorOne
- Access to the set of OneLogin credentials generated by following the instructions above
Follow these instructions to use a built-in, no-code connector hosted by ConductorOne.
In ConductorOne, navigate to Admin > Connectors and click Add connector.
Search for OneLogin v2 and click Add.
Choose how to set up the new OneLogin connector:
Add the connector to a currently unmanaged app (select from the list of apps that were discovered in your identity, SSO, or federation provider that aren’t yet managed with ConductorOne)
Add the connector to a managed app (select from the list of existing managed apps)
Create a new managed app
Set the owner for this connector. You can manage the connector yourself, or choose someone else from the list of ConductorOne users. Setting multiple owners is allowed.
If you choose someone else, ConductorOne will notify the new connector owner by email that their help is needed to complete the setup process.
Click Next.
Find the Settings area of the page and click Edit.
In the OneLogin domain field, enter your OneLogin domain, which is found in the URL of your OneLogin instance:
<YOUR DOMAIN>.onelogin.com.In the OneLogin client ID field, enter the client ID.
Paste the client secret into the OneLogin client secret field.
Optional. If desired, click to enable Sync privileges.
Click Save.
The connector’s label changes to Syncing, followed by Connected. You can view the logs to ensure that information is syncing.
That’s it! Your OneLogin connector is now pulling access data into ConductorOne.
Follow these instructions to use the OneLogin connector, hosted and run in your own environment.
When running in service mode on Kubernetes, a self-hosted connector maintains an ongoing connection with ConductorOne, automatically syncing and uploading data at regular intervals. This data is immediately available in the ConductorOne UI for access reviews and access requests.
Step 1: Set up a new OneLogin connector
In ConductorOne, navigate to Connectors > Add connector.
Search for Baton and click Add.
Choose how to set up the new OneLogin connector:
Add the connector to a currently unmanaged app (select from the list of apps that were discovered in your identity, SSO, or federation provider that aren’t yet managed with ConductorOne)
Add the connector to a managed app (select from the list of existing managed apps)
Create a new managed app
Set the owner for this connector. You can manage the connector yourself, or choose someone else from the list of ConductorOne users. Setting multiple owners is allowed.
If you choose someone else, ConductorOne will notify the new connector owner by email that their help is needed to complete the setup process.
Click Next.
In the Settings area of the page, click Edit.
Click Rotate to generate a new Client ID and Secret.
Carefully copy and save these credentials. We’ll use them in Step 2.
Step 2: Create Kubernetes configuration files
Create two Kubernetes manifest files for your OneLogin connector deployment:
Secrets configuration
# baton-onelogin-secrets.yaml
apiVersion: v1
kind: Secret
metadata:
name: baton-onelogin-secrets
type: Opaque
stringData:
# ConductorOne credentials
BATON_CLIENT_ID: <ConductorOne client ID>
BATON_CLIENT_SECRET: <ConductorOne client secret>
# OneLogin credentials
BATON_ONELOGIN_CLIENT_ID: <OneLogin client ID>
BATON_ONELOGIN_CLIENT_SECRET: <OneLogin client secret>
BATON_SUBDOMAIN: <OneLogin domain (YOUR DOMAIN.onelogin.com)>
# Optional: include if you want ConductorOne to provision access using this connector
BATON_PROVISIONING: true
# Optional: include if you want ConductorOne to sync OneLogin privileges data
BATON_PRIVILEGES_ENABLED: true
See the connector’s README or run --help to see all available configuration flags and environment variables.
Deployment configuration
# baton-onelogin.yaml
apiVersion: apps/v1
kind: Deployment
metadata:
name: baton-onelogin
labels:
app: baton-onelogin
spec:
selector:
matchLabels:
app: baton-onelogin
template:
metadata:
labels:
app: baton-onelogin
baton: true
baton-app: onelogin
spec:
containers:
- name: baton-onelogin
image: ghcr.io/conductorone/baton-onelogin:latest
imagePullPolicy: IfNotPresent
envFrom:
- secretRef:
name: baton-onelogin-secrets
Step 3: Deploy the connector
Create a namespace in which to run ConductorOne connectors (if desired), then apply the secret config and deployment config files.
Check that the connector data uploaded correctly. In ConductorOne, click Applications. On the Managed apps tab, locate and click the name of the application you added the OneLogin connector to. OneLogin data should be found on the Entitlements and Accounts tabs.
That’s it! Your OneLogin connector is now pulling access data into ConductorOne.
What’s next?
If OneLogin is your company’s identity provider (meaning that it is used to SSO into other software), the connector sync will automatically create applications in ConductorOne for all of your SCIMed software. Before you move on, review the Create applications page for important information about how to set up connectors for the SCIMed apps.