Set up an OneLogin connector
📜 Deprecation warning: A newer version of this integration is available. This version of the integration is no longer available for installation. If you’re setting up a OneLogin integration with ConductorOne for the first time, use the v2 version of the integration.
Capabilities
Sync user identities from OneLogin to ConductorOne
Resources supported:
- Roles
- Application assignments
Provisioning supported:
- Role assignment
Add a new OneLogin connector
This task requires either the Connector Administrator or Super Administrator role in ConductorOne.
In ConductorOne, click Connectors > Add connector.
Search for OneLogin and click Add.
Choose how to set up the new OneLogin connector:
Add the connector to a currently unmanaged app (select from the list of apps that were discovered in your identity, SSO, or federation provider that aren’t yet managed with ConductorOne)
Add the connector to a managed app (select from the list of existing managed apps)
Create a new managed app
Set the owner for this connector. You can manage the connector yourself, or choose someone else from the list of ConductorOne users. Setting multiple owners is allowed.
A OneLogin connector owner must have the following permissions:
- Connector Administrator or Super Administrator role in ConductorOne
- Administrator or account owner access to your OneLogin account
- Click Next.
Next steps
If you are the connector owner, proceed to Configure your OneLogin connector for instructions on integrating OneLogin with ConductorOne.
If someone else is the connector owner, ConductorOne will notify them by email that their help is needed to complete the setup process.
Configure your OneLogin connector
A user with the Connector Administrator or Super Administrator role in ConductorOne and Administrator or account owner access to your OneLogin account must perform this task.
Step 1: Locate your OneLogin domain
Look up your OneLogin domain, which is found in the URL of your OneLogin instance:
<YOUR DOMAIN>.onelogin.com.Make a note of your domain. We’ll use it in Step 3.
Step 2: Create an API credential
Sign into OneLogin as an Account owner or Administrator.
Navigate to Developers > API Credentials.

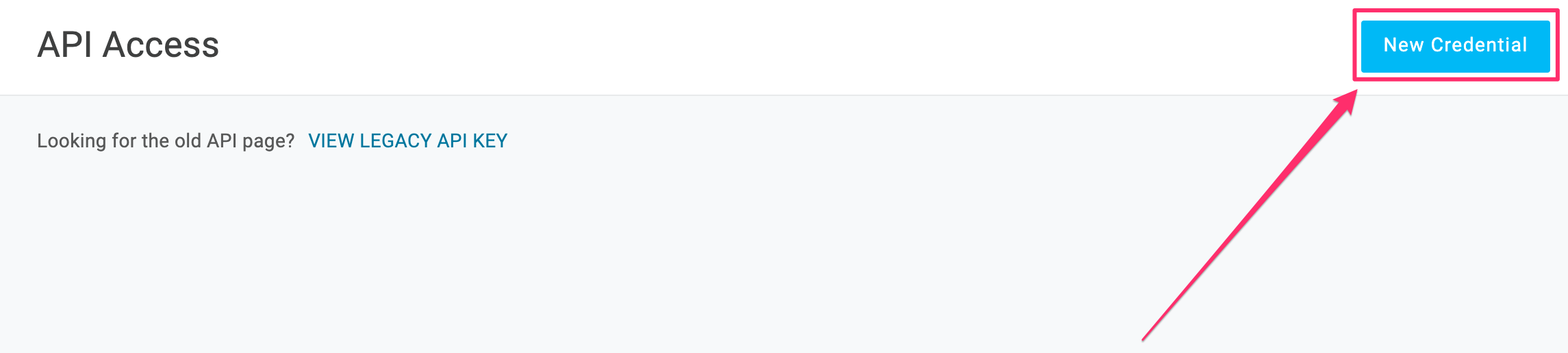
Click New Credential
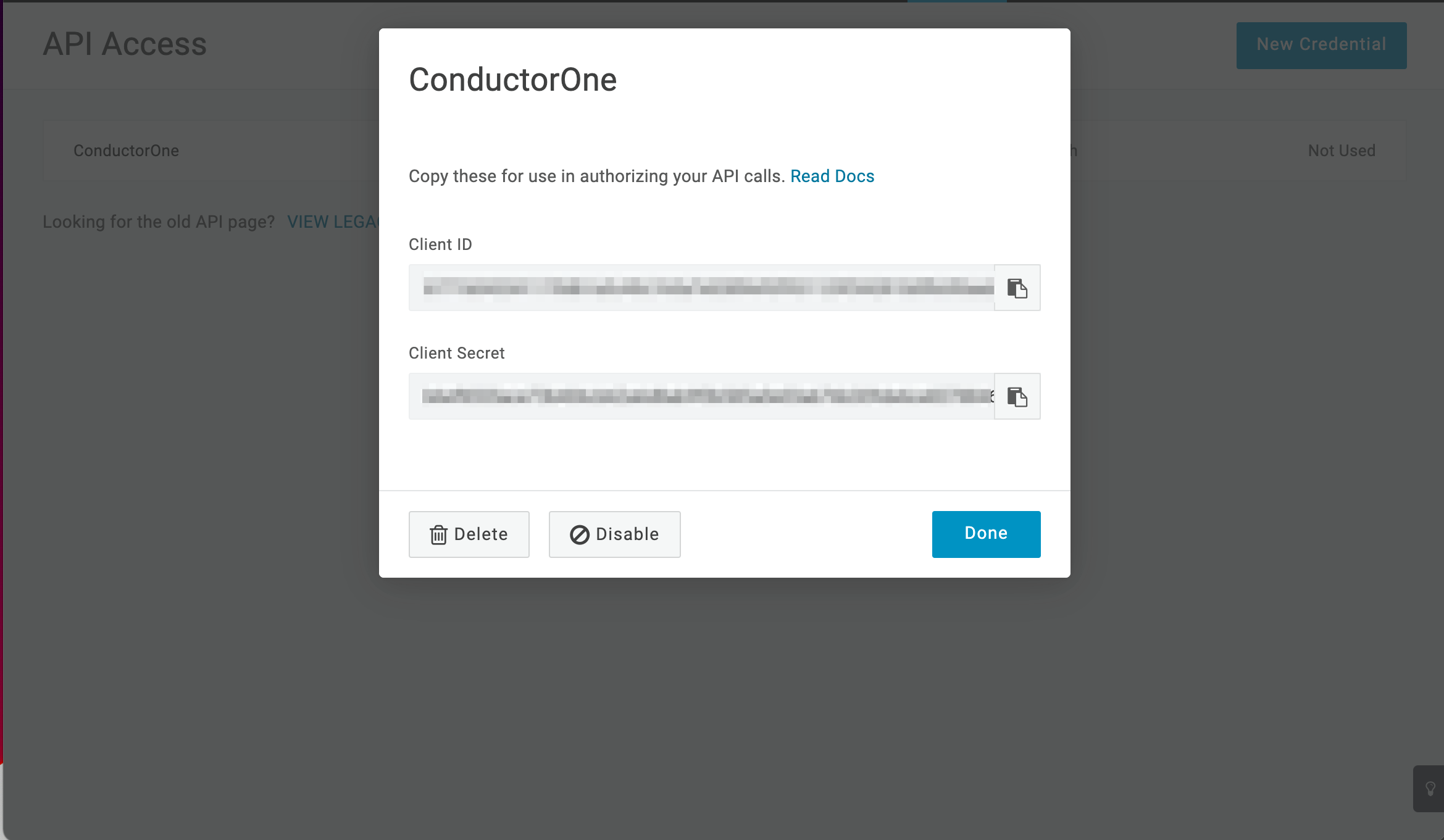
Give the API credential a name, such as ConductorOne.
Select the Manage all scope.
Click Save.
When the new API credential is created, copy and save the Client ID and Client Secret. We’ll use these in Step 3.
Step 3: Add your OneLogin credentials to ConductorOne
In ConductorOne, navigate to the OneLogin connector by either:
Clicking the Set up connector link in the email you received about configuring the connector.
Navigate to Connectors > OneLogin (if there is more than one OneLogin listed, click the one with your name listed as owner and the status Not connected).
Find the Settings area of the page and click Edit.
In the OneLogin domain field, enter the domain you looked up in Step 1.
In the OneLogin client ID field, enter the client ID from Step 2.
Paste the client secret from Step 2 into the OneLogin client secret field.
Click Save.
The connector’s label changes to Syncing, followed by Connected. You can view the logs to ensure that information is syncing.
That’s it! Your OneLogin connector is now pulling access data into ConductorOne.
What’s next?
If OneLogin is your company’s identity provider (meaning that it is used to SSO into other software), the connector sync will automatically create applications in ConductorOne for all of your SCIMed software. Before you move on, review the Create applications page for important information about how to set up connectors for the SCIMed apps.
Configure the OneLogin integration using Terraform
As an alternative to the integration process described above, you can use Terraform to configure the integration between OneLogin and ConductorOne.
See the ConductorOne OneLogin integration resource page in the ConductorOne Terraform registry for example usage and the full list of required and optional parameters.